A Horde of 4.5 Million Zombie Computers Is Marching Towards You

Share
It's name is TDL-4, and they say it's invulnerable. Known as a botnet, this malicious software has infiltrated an estimated 4.5 million PCs around the world, using them without their owner's knowledge and turning them into the silicon equivalent of zombies. There are many active botnets, and many more have been defeated by anti-virus security firms, but TDL-4 is special - it's advanced. This cutting edge botnet can remove competing malware, install malware of its own, and rent out its network for spamming or phishing ventures. It communicates on multiple channels, with millions of infected computers receiving commands over public peer to peer (P2P) networks. TDL-4 even buries itself in the master boot record, making it invisible to your operating system and security software. In short, TDL-4 is one of the most sophisticated pieces of malicious software that has ever been put forth on a global scale, and it's just getting warmed up.
The TDSS botnet aka TDL has been active since 2008, with the latest version, TDL-4, probably launching in the last year. Malware tracking groups like Dell Secure Works, Trend Micro, and Symantec have all done their best to deal with it. Kaspersky Labs has perhaps the most detailed public report on the botnet, with estimates for its size, deployment, and propagation techniques. Through its development, TDL has incorporated all the latest tricks it can find, including some developed by the Stuxnet worm, a military grade virus (probably developed by the US or Israel) aimed at disabling Iranian nuclear facilities.
TDL-4 is upgraded to take advantage of the latest 64 bit computer architectures, and has evolved to communicate through Kad, a public P2P network. Able to receive instructions and upgrades via command and control servers, or through the public P2P networks, TDL-4 zombie computers are that much more resistant to be detected, and removed. Even more impressive, computers infected with the TDL-4 botnet will actually remove other forms of malicious software (up to 20 different breeds, according to Kaspersky), making them less suspicious to anti-viral programs. TDL isn't just a criminal, it's a crime boss that protects its territory viciously.
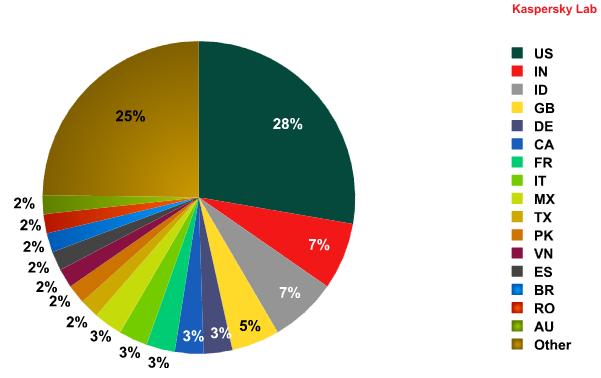
Kaspersky Lab estimates for TDL-4 infection around the world. While more than a quarter of TDL zombies are in the US, the network is spread wide, making it even harder to take down.
Why put so much effort into creating a nigh invulnerable botnet? Money, pure and simple. The TDL-4 network is most likely rented out at a high price to criminal organizations. With 4.5 million zombie PCs working for them, the owners of TDL-4 can launch impressive spamming and phishing campaigns which can rake in huge profits. Or, TDL-4 can be used to plant other malicious pieces of malware, including spybots, hijacking toolbars, and even fake antivirus software! Kaspersky puts the number of such associated malware programs at around 30. When a contract runs out, TDL-4 can remove these programs easily. Remember, TDL-4 is also removing the competition (malware it doesn't sanction) while opening your computer to the evil software it prefers. If this was taking place on the streets instead of the internet, we'd call it a mafia war. It's definitely the cyber version of organized crime.
The continual development of this network, its advanced tactics, and its wide dispersal all point to TDL-4 being the work of a concentrated criminal network with hundreds of thousands (if not millions) of dollars devoted to development of its cyber empire. In fact, Kaspersky recently detailed one way in which the botnet was spreading. "Partner-programs", most often operating through websites offering adult content, bootleg videos, or file storage, are paid $20-$200 for every 1000 computers they infect with TDL. Kaspersky estimates that TDL-4 has cost its creators about $250,000 to set up their network. That's a big investment, but one it's going to make back very quickly. Daily revenue from a botnet the size of TDL-4 can be in the many tens of thousands of dollars.

How a Botnet Works: 1. Botnets hide in trojan horses, innocuous pieces of software containing the malicious code. 2. After being infected, your computer is a botnet zombie, awaiting its master's commands. 3. Criminals pay the botnet owner to do their bidding. 4. The horde of zombie computers attack! Step 5: PROFIT! Image Credit: Privacy Canada
Be Part of the Future
Sign up to receive top stories about groundbreaking technologies and visionary thinkers from SingularityHub.


It's important to keep in mind that while several experts have called TDL-4 'indestructible' and 'invulnerable', the global community of security software engineers has taken down larger botnets in the past. TDL-4 might not even be the most dangerous piece of malware out there, as its owners seem to be seeking profit rather than wanton destruction. What really worries me about TDL isn't that it will be so hard to beat, it's that it represents the new paradigm in the attitudes of many malware creators. This network represents a long term and ongoing investment. TDL isn't a fly-by-night get rich quick scheme (well, not exclusively), it's a concentrated effort to build a valuable commodity that will pay dividends for years to come. Its very history of upgrades (TDL, TDL-2, TDL-3, TDL-4) suggests that its creators are in this for the long haul. Look at the TDL-4 business plan: pay subcontractors to install the code on computers, eliminate competition and keep a low profile, rent out the network for profit, remove traces of use to keep a low profile, and wait for the next profit opportunity. Those are the same tactics you might see in any aggressive and exploitative industry.
We've seen how governments are investing in cyber warfare as a necessary part of their military arsenal. TDL-4 shows us the same is true for organized crime. As malware has grown more sophisticated, it has become a sort of shadow industry whose products are as impressive as they are evil. Undoubtedly, the distinction between cyber warfare and cyber crime is going to blur, with tactics developed in one arena being adapted for the other and vice versa (as TDL did with Stuxnet). I have a lot of faith in the thousands of security experts who will help protect the common user against botnets and their malware brethren. Hopefully their efforts will stay one step ahead of the criminal programmers behind these mighty botnets...but it might be a very close race.
[image credits: Privacy Canada, florisla via Wikicommons (modified), Kaspersky Labs, Tom-B via Wikimedia, ]
Sources: kaspersky labs
Related Articles

Sony’s Table-Tennis Robot Beat Elite Human Players With Unorthodox Moves

Printed Neurons That Mimic Brain Cells Could Slash AI’s Energy Bill
MIT Mined Bacteria for the Next CRISPR—and Found Hundreds of Potential New Tools
What we’re reading