Al Qaeda In Azeroth? Terrorism Recruiting and Training in Virtual Worlds

Share
In their pursuit of terrorists, government intelligence agencies leave no digital rock unturned: telephone calls, emails, text messages, blogs, news sites - they monitor them all. Sometimes, as with social networks like Facebook, the companies behind these services gladly hand over data to governments to assist in this hunt. Yet there is still one place where terrorists can go, one place where they can talk to each other openly without fear of being detected: online video games. Hundreds of millions of people flock to massively multiplayer online role playing games like World of Warcraft, and revel in online virtual worlds like Second Life. ...and somewhere in those millions are terrorists looking to plot the next big attack against Western civilization. That's right, terrorism has been chased into using virtual reality as its staging grounds. The future is a strange, comical, and scary place to live when that Level 40 Night Elf looking for a group may be Al Qaeda in disguise.
The US Intelligence Advanced Research Projects Activity (IARPA) has been aiming to trace criminal and terrorist activities perpetrated online. Started in 2008, their "Project Reynard" is specifically geared towards uncovering recruiting and training operations going unnoticed in online gaming environments. Check out the news story explaining Project Reynard in the video below. While the IARPA project is unlikely to produce publicly accessible results anytime soon, anxiety over the use of virtual reality for terrorism is already increasing. The recent bombing and massacre in Norway, and a Dutch best selling novel have also heightened the public awareness of terrorists benefiting from online games. Yet even if terrorists can be found in virtual reality the way they have been found in every other communication system, will kicking them out really end their operations?
That terrorists have infiltrated online games is no longer largely questioned. The US National Intelligence director acknowledged the threat in his Data Mining Report in 2008. This is a real phenomenon, a real "threat to national security", and that blows my mind. When did hard-line killers get together and say, "you know where we can organize our attacks? The same place where nerds go to pretend to be superheroes and kill bad guys." The irony there is palpable. What remains to be seen, however, is if governments will be able to accurately quantify the size of this threat, and neutralize it. That's where Project Reynard comes in, as Bill Moyers explains:
Bill Moyers' coverage of IARPA's Reynard gets a little hyperbolic (suddenly 2008 seems like a lifetime ago) but the concerns over the breadth of the project are real. Documentation for Reynard shows that the goal isn't so much to find specific terrorist cells using specific online platforms, it's to develop a way of discovering any kind of suspicious behavior occurring in these virtual realities. Essentially, IARPA wants to have a reliable means of quantifying the way characters act in these games so that they can draw reasonable conclusions about the people controlling those avatars. What does the guild you join on World of Warcraft, the shops you frequent in Second Life, and the characters you chat with reveal about your nationality, your economic status, and your inclination towards real world violence? It's a little funny (weird, not ha-ha) to think of terrorists resorting to online video games as secret hideouts, but it's considerably less so to consider governments will now be trolling through everyone's game statistics to find those criminals.
By the way, if connecting digital behavior to personality traits seems like a foolish endeavor, remember that scientists are finding ways to translate the smallest facial tics and physical gestures into profiles to find terrorists entering public locations like airports. With enough data, even virtual clues may be able to reliably identify groups with terrorist associations. From there, it's just a matter of data mining and analysis to determining who is "suspicious" and when and where they are gathering. The same basic approach is already used to cull through millions of emails, phone calls, and text messages.
Project Reynard launched in the last quarter of 2009 and is set to conclude sometime next year. It will join other online intelligence gathering operations, like the EU's much larger Project Indect, aimed at combing through huge amounts of data looking to find evidence of criminal or terrorist activity. While there have been noted examples of terror organizations like Al Qaeda recruiting members through email, porn sites, and other internet forums, considerably less is known about recruitment and training in online games. That's because so much that happens in those virtual worlds is simply unmonitored...for now. While privacy terms for most virtual worlds like Second Life make it clear that your actions in most online environments is considered public, most of us can converse freely without worrying about government eavesdropping. Reynard (and to some extent, Indect) may change that. While we've grown accustomed (or oblivious) to the automated sifting through our mobile calls, emails, and text messages, it's going to be extra creepy to think that IARPA may be tracking who I talk to while role-playing a giant anthropomorphic panda.
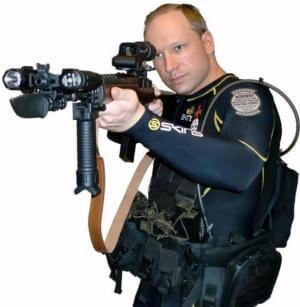
Not the good kind of cosplay. Maniacs like Breivik will always be with us, and for now virtual games may hold an appeal for them. But we shouldn't blame games for Breivik anymore than we should blame J.D. Salinger for John Lennon's death.
Even before Reynard is ready to share its results, crime fighting organizations in the US have already taken up monitoring online gaming to catch illegal activities. According to documents captured by LulzSec, and released on Public Intelligence, New Jersey and New York authorities (in cooperation with the FBI) have monitored conversations made by gang members on the Play Station 3 and Xbox 360 consoles related to past and future crimes, some international. It seems gangs figured out that most voice over internet protocols would largely go unexamined. While clearly that is less true than they assumed, VOIP is probably still a safer bet for clandestine activities than landlines and mobile phones. In-game discussions, say in a rousing match of Halo may be even more difficult to pin down at the moment. I'm sure police and criminals are learning what Reynard already assumes - anytime you have a virtual location that enables one-to-one communication, you have the possibility of its use for facilitating illegal activity.
Of course, some people don't even need the one-to-one communication to help them commit terrorist atrocities. Anders Behring Breivik, the gunman responsible for killing dozens of children and camp staff in the recent attack in Norway, left a massive manifesto describing his motivations and preparations. Apparently the fiend used Call of Duty: Modern Warfare 2, which has many realistic depictions of 21st Century military operations, as a training ground for his attack. Reactions to Breivik's use of online gaming has provoked a wide range of reactions, from condemnations among gaming communities to knee-jerk calls for banning all sales of the game in Europe. No matter how you feel about violence in video games, however, Breivik's activities suggest the possible uses terrorists may find in virtual worlds without using them for communication.
Be Part of the Future
Sign up to receive top stories about groundbreaking technologies and visionary thinkers from SingularityHub.



An international best seller, MMORPG raises concerns about how terrorists could easily use online gaming to recruit and train operatives. Of course, Dan Brown raised similar concerns about albinos and the offspring of Jesus so...
Dutch author Emile van Veen is far less subtle, preferring to outline exactly how terrorists can use video games to kill us all. His international best seller, MMORPG, is a Dan Brown-esque thriller wherein a duo of unlikely heroes must race against the clock to unveil a hidden terrorist plot centered around the use of a massively multiplayer online game. Schlocky? Yeah, maybe, but since its release in March of this year, van Veen's MMORPG has raised public awareness of the links between terrorism and online gaming to new heights. Based on "two years of research" into the realities of virtual assisted terrorism, MMORPG paints a grim picture. Aided by the anonymity and accessibility of online gaming, terrorists can talk to each other almost anywhere, anytime, without the threat of being detected. At least, in van Veen's fiction. It's scary to contemplate that the same may be equally true in the real world.
As always with the ongoing "War on Terror", the risks and defenses seem almost equally horrible. Clearly some lunatics will use video games as inspiration or preparation for their murder sprees. I doubt we'll ever be able to stop that completely - such crazies will always find something to fuel their need to hurt people. What's both more concerning, and more controllable, is the use of virtual worlds as staging grounds for organized terrorist attacks. It's disturbing to think that the only solution proffered to fight such organizations is a reduction of everyone's privacy while playing these MMORPGs. The loss of freedom to fight the loss of life seems like a zero sum game to me.
Yet it's also the only game intelligence agencies seem to want to play. Before we sign over all privacy in virtual reality, we should remind our governments that while online games may temporarily provide ideal circumstances for terrorists to communicate, the advantages there won't remain unique. Any virtual location where people can go unmonitored is going to be a problem. Even if Project Reynard effectively closes virtual games to terrorism, another such online opportunity will arise. Trolling World of Warcraft for terror cells may be necessary, but it's a short term fix. Ultimately we're going to have to fight the sources of these movements (both in the real and virtual worlds) if we're to have any hope of them ending.
Image credits: erwin franzen, emile van veen, andrew berwick
Sources: iarpa, emilevanveen.com, public intelligence
Related Articles

In the Scramble to Power AI, Investors Bet $140 Million on Data Centers at Sea
Quantum Computers Are Coming to Break Cryptography Faster Than Anyone Expected

Printed Neurons That Mimic Brain Cells Could Slash AI’s Energy Bill
What we’re reading

