Dick Cheney Took Heart Defibrillator Offline in 2007 to Guard Against Hackers
In a recent “60 Minutes” interview, former Vice President Dick Cheney said his cardiologist turned off his defibrillator’s wireless functionality to protect against a potential attempt on his life—by hacking his heart.
Share
In a recent “60 Minutes” interview, former Vice President Dick Cheney said his cardiologist turned off his defibrillator’s wireless functionality to protect against a potential attempt on his life—by hacking his heart.
Cheney, not exactly the poster child of heart healthy behavior, at one point smoked three packs of cigarettes and ate a dozen donuts daily. He’s had five heart attacks and, recently, a heart transplant. Doctors implanted a new defibrillator in 2007.
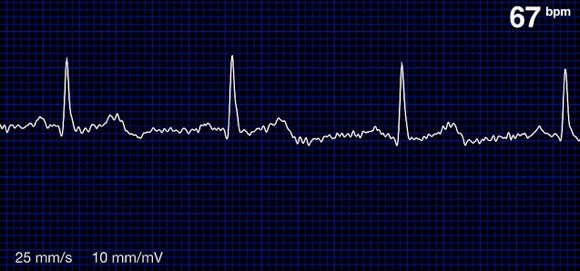
Such devices detect frenzied heartbeats and are capable of delivering a shock to bring them back to a more normal cadence. They often use a wireless connection to connect to the Internet so cardiologists can remotely monitor their patients.
In 2007, Cheney’s cardiologist, Dr. Jonathan Reiner made sure the manufacturer disabled the wireless feature so a terrorist couldn’t remotely gain control of the implant and deliver a fatal shock to Cheney’s heart.
Dr. Reiner said, “It seemed to me to be a bad idea for the vice president to have a device that maybe somebody on a rope line or in the next hotel room or downstairs might be able to get into—hack into.”
In addition to pacemakers and defibrillators, other connected medical devices include insulin and drug infusion pumps, patient monitoring equipment, ventilators, and anesthesia delivery equipment. In coming years, we may use smartphones to diagnose conditions and otherwise monitor our health.
Clearly, there are a rapidly increasing number of medical devices coming online. But security concerns are nothing new. Experts have noted the problem for years.
As far back as 2008, it was known that a defibrillator like Cheney’s was vulnerable to attack. The New York Times reported that researchers in a lab were able to gain control of a Medtronic device and shut it down or send fatal shocks.
In 2011, Singularity University’s Chair for Policy, Law and Ethics and Global Security Advisor, Marc Goodman, noted, “The rapid advances in medical technology, paired with the relative paltry consideration of security in medical devices, should be a wake-up call for those that build and implement these life-saving technologies.”
Be Part of the Future
Sign up to receive top stories about groundbreaking technologies and visionary thinkers from SingularityHub.


Manufacturers and healthcare professionals have long known of the risks, but devices remain vulnerable. Just this June, the US Food and Drug Administration (FDA) issued a warning to device-makers, hospitals, and patients, advising all parties to take care and better secure their devices.
Although, the FDA said it had no records of patient injury or death due to a hacked or infected medical device, they’ve been notified of numerous incidents in the last year involving “hundreds of medical devices” and “dozens of manufacturers."
The FDA further cited research by security firm Cylance, Inc., that uncovered some 300 poorly secured medical devices. One of the report’s authors, Billy Rios, later said a key problem is the use of default passwords that are easily discovered by hackers.
Worse, you may not even need to be an adept hacker to gain access. A search engine called Shodan trawls the Internet for online devices whose access is often guarded by no more than an IP address. Apart from infrastructure, like power plant controls and office building systems, Shodan has found fetal heart monitors and glucose meters.
We often write about the good a smarter, more connected world might bring, but there’s always a dark side to be exploited.
As Goodman went on to note, “While the development of these technologies will surely alleviate human suffering and disease, unless the important security-related issues of integrated human-machine interaction are addressed, society may be confronted with a whole new meaning for the term ‘heart attack.’”
Image Credit: Juhan Sonin/Flickr, MilitaryHealth/Flickr
Jason is editorial director at SingularityHub. He researched and wrote about finance and economics before moving on to science and technology. He's curious about pretty much everything, but especially loves learning about and sharing big ideas and advances in artificial intelligence, computing, robotics, biotech, neuroscience, and space.
Related Articles

Sodium Is Cheap, Abundant, and Now Powering Batteries That Could Rival Lithium
An AI Solution to an 80‑Year‑Old Problem Has Shocked Mathematicians

Photosynthetic Drops Soothe Dry Eyes With Sunlight
What we’re reading